Check the bank details
Three clients hit by "someone changed the bank details on an email" fraud, over £2m diverted and lost. Are you safe?
Three clients have lost large sums in the last few months. All are sophisticated companies with good governance and strong internal controls. Total cash lost now exceeds £2,000,000
None of them knew the money was gone for several days. By the time they knew, it was too late: the cash had been split up and “layered” away to overseas bank accounts beyond reach.
The reaction of banks was the same in each case “we have no liability to you and we will not give you any details of the recipient bank account”.
The reaction of the police was the same in each case “here is a standard email”. They have no resources and have no incentive to help companies recover funds.
When they go to their lawyers, they learn that the cost of a legal process to chase their funds might exceed the amounts lost. It is almost certainly too late to use the cheaper and faster “freezing orders” (used to be called “Mareva Injunctions”)
The reaction of insurers is usually positive, but only if the company had specific cybercrime insurance and had complied with all its warranties and duties. Assessing that is never as quick or cheap as one might hope. Insurers are under huge pressure as cybercrime claims are growing very fast.
So, what happened, and what can you do about it?
What happened?
By hacking into your email, scammers can intercept invoices and payment instructions. They then change the payment details of individuals and businesses to bank accounts they control.
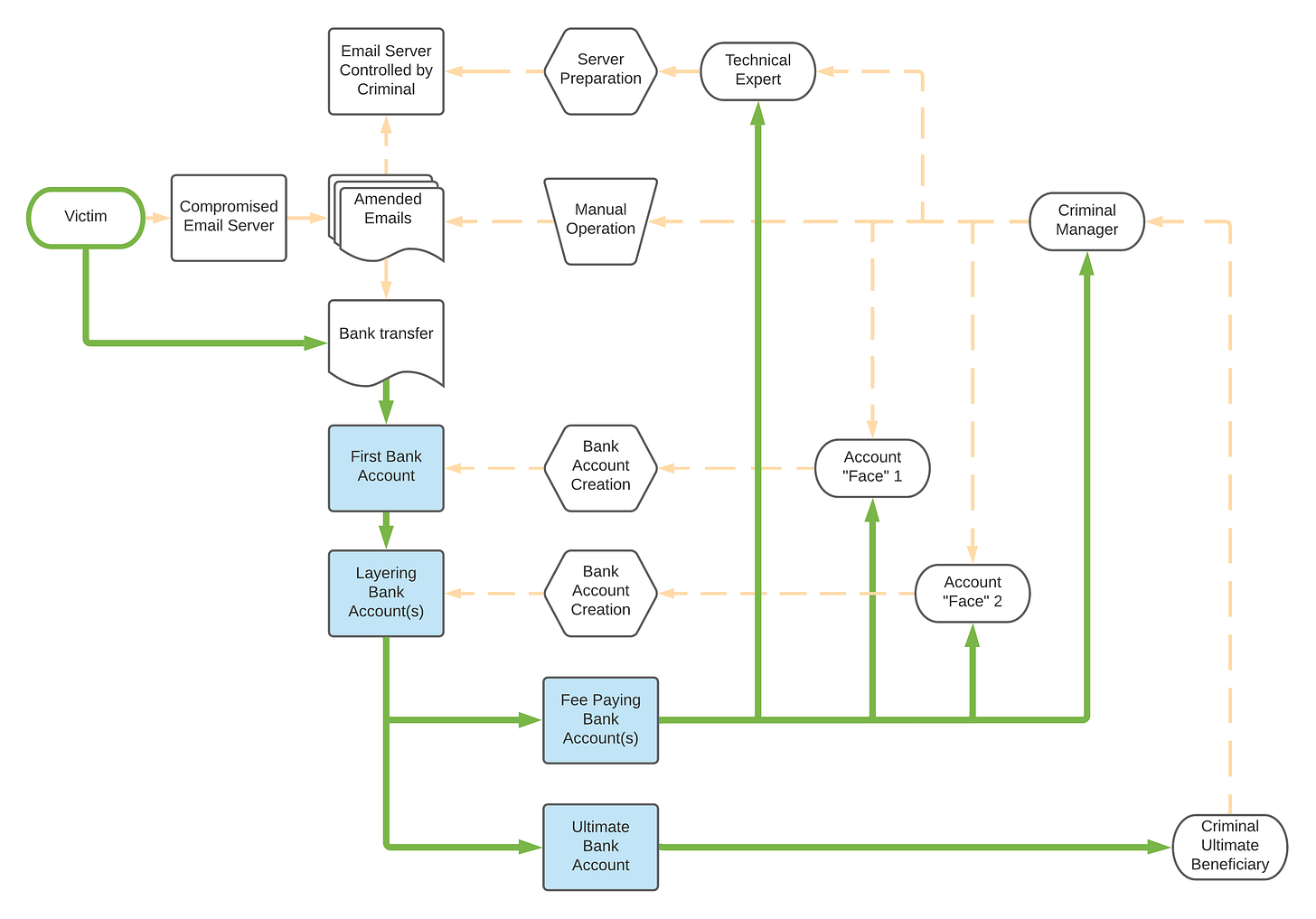
That is the simple version. That is all the client sees. Behind the scenes, a lot has been happening for a long time. I have created this little briefing image to explain:
The first event was the innocent clicking of something (usually an email attachment) which inserted a trojan into your email system or, more rarely, when a security weakness at the host or server level allowed an attacker to get control of your email.
Then, for ever after, all email hitting your server is diverted to their server, scanned, then sent back to your server. You see nothing, except, perhaps, a slightly longer delay in email receipt from clients. Maybe 10 minutes.
There is an excellent technical explanation here
How it should work
What criminals do to you
The criminals also have a network of “faces”, who are usually cash poor and naive individuals who are prepared to register companies and bank accounts for a fee (say (£2,000 and a free mobile phone). The favourite faces are those who are not UK citizens, with poor written English, and in rented accommodation.
The criminals constantly create and churn companies online and open bank accounts for them. those companies will never file account, and the directors and shareholders are usually just that innocent face who forwards all mail and calls to the criminals.
Then, for days, or even months, the criminals just sit there, and watch. They use their server to scan your email for keywords. Words like this: "sort code”, “bank transfer”, “send payment to”.
The risk to you is crystalised when the Criminal Manager identifies your company as one that handles large cash transactions. They wait for you to have to pay a large sum for a genuine purchase, often a large capital item or land or company acquisition. (The smallest theft I have seen was £25,000 which is well below the average “trigger level” of around £1,000,000. At that point, the fraudsters switch into an active attack.)
The active attack requires the criminals to scan for and intercept a specific email. They like to work with plain text email, but can work with Microsoft Word invoices, PDF invoices, and even online (e-invoice) services if they need. They
What can you do?
Make a director responsible for the risk of payment fraud of this nature.
https://fraudwatchinternational.com/phishing/email-security-mx-records/
Check your email server right now and then once a week. Send your head of IT and your Managed Service Provider to these websites and demand they explain how you are being protected, what reports prove that, and what they will do and how fast they will do if you suffer a fraud of this nature
https://elie.net/blog/security/how-email-in-transit-can-be-intercepted-using-dns-hijacking/
https://blog.mxtoolbox.com/category/knowledgebase/fraud-and-phishing/
https://postmarkapp.com/guides/spf
Educate all staff about the risks.
Conduct detailed due diligence on all payees using public registers and credit rating agencies. Check out the companies, directors, and check the bank they claim to bank with (a £1 transfer that is returned to you). Then make it standard operating procedure to double check every spelling, postal address, email, bank account, email, company number, and name for all major suppliers or contract partners on a regular basis. The more often you check, the more likely you are to spot subtle changes. (In several cases I know, there were ‘cheeky’ changes to company names or sender names as well)
(Hot tip - run your payment database against your payroll database. It is not unknown for a member of staff to let their bank account get used in payment frauds either!)
Take out cyberfraud insurance and stick to the conditions.
Do NOT under any circumstances change payment details in response to an email without checking verbally with the customer or contract partner using a phone number that you already have on file and have used before.
When making large payments, first make a small one (£1 to £10 and the odd pennies are part of the test) and ask them what amount was received, then ask them to send it back to you. Check the bank details. Pay the fees with a smile. Confirm with someone you know and trust on the phone or in a video chat.
If there is extreme time pressure (there should never be, of course!), then confirm on video conference with a “triangle” of parties - you, the intended recipient, a third party you trust who knows and can identify the intended recipient. Check all numbers on screen.
Make your solicitors do this as well - solicitors are a major target of this sort of scam.
What if the worst happens
Act fast.
call your lawyers, and get a freezing injunction against the bank or banks that received the cash
call the recipient banks and put them on notice, insist their Head of Fraud gets involved
alert your email provider and shut the server, revoke all access until resolved, back it and all the logs up to a secure site, change passwords, change admins, and start again on a secure basis. Those logs and copies may be the evidence that convicts or secures recovery.
alert your insurer
inform the police
my personal view is that you should go public - you may not save yourself, but you can save others. This crime has been spreading because people want to “protect their reputation”, which is fine, but the best defence is an alert business community that works together to stamp out crime. Your head of brand might have other ideas, but you can make the argument to them.
No defence is perfect
There are always variants of this that can take your money, even if you do all these things. You can only reduce the risk and reduce the impact.
We can help design and implement systems that can reduce the risk.
We have been involved in a dozen asset tracing cases as Forensic Accountant and as Computer Forensic Expert and as Investigating Accountant. Partnering with lawyers, insurers, banks, and law enforcement, my experience is that we can obtain a better outcome all around for our clients where we act in the centre to coordinate, inform and advise.
The clients who were hit came to us late, but are now working with us on security, recovery, and education projects. The steps above would have protected them completely from the frauds they were victims of.
Do you have advice or experience to share?